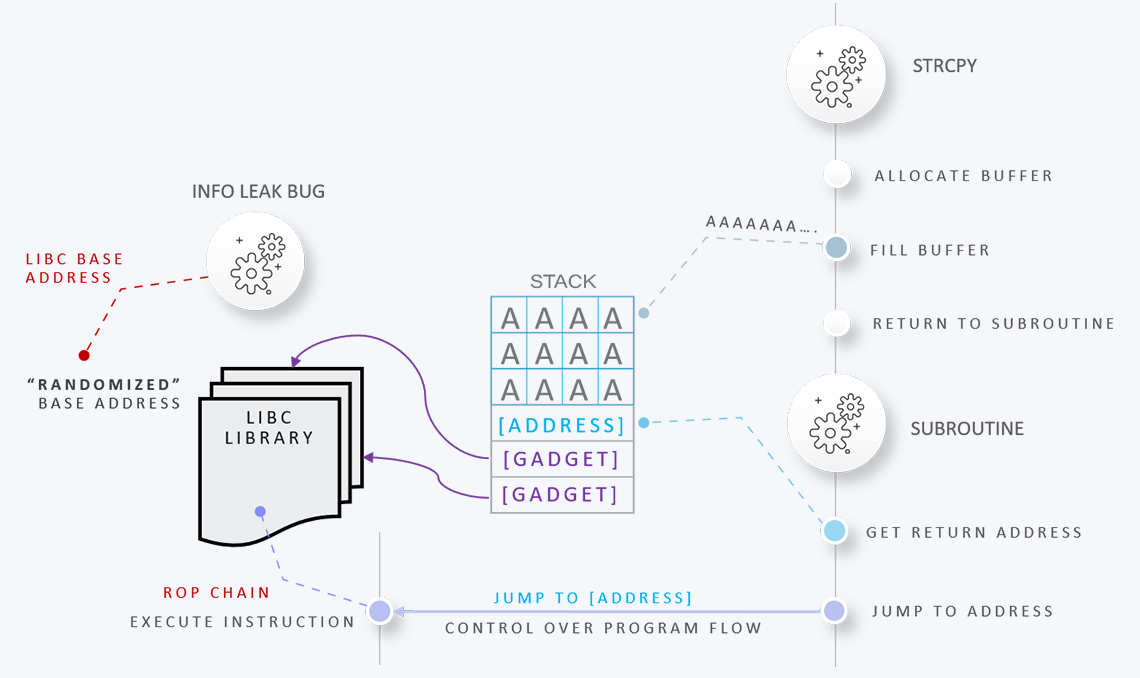
Services
Private Training
Book one of our high-quality private training courses delivered online or on-site with a minimum class size of 10 participants.
Learn More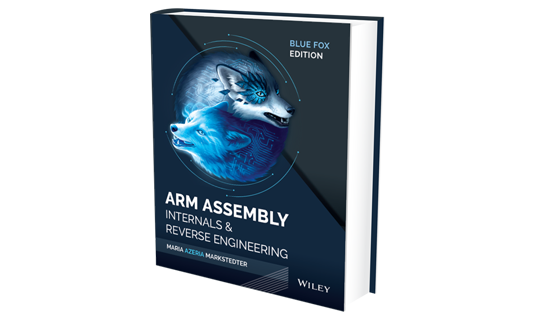
Book
Level up your Arm assembly knowledge with Azeria's best-selling book Blue Fox: Arm Assembly Internals and Reverse Engineering.
Purchase Book
Public Speaking
Request Azeria for public speaking engagements at public or private events, including keynotes, panels, internal events.
On Hold